Apr 24, 2024
What do an art gallery, a global automobile manufacturer, a power management company, and a government agency have in common?...
Apr 12, 2024
In 2024, most federal agencies and companies are prioritizing the following initiatives: Improving customer experience (CX) through rapid response and...
Feb 29, 2024
A generic e-commerce channel is no longer enough for B2B companies looking to grow their business in today's economy. To...
Feb 20, 2024
When a company first decides to move their commerce platform and supporting toolsets to a new ecommerce platform, they typically...
Feb 15, 2024
Companies that invest in B2B commerce can maximize potential revenue and boost their competitive advantage. B2B commerce, or business-to-business electronic...
Feb 1, 2024
Every day, more and more companies are moving their intellectual property and sensitive data to the cloud environment and taking...
Jan 12, 2024
A major component of digital transformation for many organizations is migrating to the cloud. Even when only a part of...
Jan 9, 2024
Every organization mapping out a cloud migration strategy wants to facilitate a smooth, trouble-free ascent to the cloud infrastructure. But...
Jan 8, 2024
Migrating workloads, applications, and data from on-prem hosting to the cloud offer the potential to drive cost savings for your...
Jun 21, 2023
Picture this: You've got a solid team of developers building out a new application for the organization. The product manager...
May 24, 2023
Any organization that has had to simultaneously tap multiple managed services vendors knows the challenges that come with such an...
May 17, 2023
The insurance industry is undergoing rapid change, with emerging risks like ESG, cryptocurrency, and cybersecurity intersecting with systemic challenges such...
May 16, 2023
Combining Technical Capabilities with Business Perspectives to Enable Underwriting Craftmanship for Complex Risks In our last post, we discussed low-complexity...
May 15, 2023
As the insurance industry evolves, underwriting organizations are under pressure to make more informed decisions and stay competitive in the...
May 12, 2023
How a Strong Data Foundation Fuels Your Underwriting Innovation Strategy As the insurance industry evolves, it is becoming more crucial...
May 9, 2023
A look across the post-pandemic healthcare landscape underscores this reality: Public health is the product of an integrated --...
May 3, 2023
Meaningful member engagement that puts the customer's needs first is foundational to any effort to increase adherence to care plans. ...
Apr 7, 2023
As a health insurer advances its care quality and engagement strategy beyond correcting immediate health conditions toward long-term preventative...
Mar 20, 2023
Ask insurance payers if they would rather cover preventative care or reactive treatment and they’ll tell you (kindly, of course)...
Mar 9, 2023
In part 1 of this series we talked about the evolving state of complex P&C insurance risk management. In...
Mar 6, 2023
While risk management is at the core of any property and casualty (P&C) insurance company, the rapid pace of...
Feb 16, 2023
Patient noncompliance is a costly reality that insurance payers are all too familiar with. Foregoing annual wellness exams and physicals,...
Feb 13, 2023
In the Pharma and Life Sciences sector, mobile applications have the potential to unlock efficiencies, increase revenue streams and drive...
Feb 7, 2023
In the latest episode of DMI’s podcast Beyond DigitaI, Amy Barger, DMI’s Vice President of Digital Business Solutions, and Josh...
Jan 24, 2023
Advances in automation capabilities, artificial intelligence, and machine learning are providing insurers new opportunities to reduce their loss ratios through...
Jan 17, 2023
The leaders in your insurance organization may understand why a product measurement strategy is critical to maximizing the impact of...
Jan 11, 2023
Let’s say your insurance organization has just embarked on a months-long agile journey to create a customer-facing digital product, such...
Dec 5, 2022
For years, digital transformation has been the go-to term for private sector modernization efforts, leaving the public sector behind....
Nov 14, 2022
Our experience at DMI has shown that Pharma and Life Sciences companies in the middle of a digital transformation wrestle...
Nov 2, 2022
As fears of a recession grow amid continuing supply chain issues and rising inflation, businesses in the retail and eCommerce...
Oct 27, 2022
Traditionally, Healthcare, Pharmaceutical and Life Science companies develop software using a “Waterfall” model. Under the Waterfall model, every stage...
Oct 19, 2022
Let’s say you lead an underwriting organization that wants to shift its focus from growth to profitability. There are certainly...
Oct 12, 2022
End-user experience is critical to the success of every business. For example, almost 90% of people say they won't shop...
Oct 7, 2022
State and local governments provide essential citizen services, operate and maintain critical infrastructure, and process and store sensitive personal...
Sep 26, 2022
The promise of digital transformation is reshaping the business world across all sectors, including the insurance industry. In practice, though,...
Sep 22, 2022
When it comes to brand building, content is key. But how do you know if the content you're producing...
Sep 20, 2022
At the Detroit International Auto Show on Wednesday, Sept. 14, Joe Bannon, DMI’s Global Vice President of Business Development, led...
Sep 12, 2022
Consumers have unlimited choice when it comes to which brands to engage with—and the power is in their hands. They...
Aug 24, 2022
Let's say your federal agency is embarking on a digital transformation project. The RFP is out. The proposals are coming...
Aug 22, 2022
Digital transformation is not a one-size-fits-all proposition. To gain the benefits and experience growth, organizations don't need to completely rebuild...
Aug 22, 2022
The Fourth Industrial Revolution has impacted every industry around the globe. Even though corporate and back office services have profited...
Aug 22, 2022
The new reality of remote and hybrid work means companies are seeing their device lifecycle management complicated by new logistical...
Aug 22, 2022
Many of the indications of an economic downturn are in front of us. Rising interest rates, drops in consumer spending,...
Aug 15, 2022
Today’s automotive manufacturers know all too well the global disruptions that put their traditional growth strategies at risk. To name...
Jul 28, 2022
Modernizing legacy applications build a government agency’s ability to be resilient and agile in the face of disruption. For over...
Jul 19, 2022
From 2023 through 2030, the global managed services market is expected to grow at a compound annual growth rate of 13.6%,...
Jul 5, 2022
As government agencies and Department of Defense (DoD) systems obtain Authorization to Operate (ATOs) for their systems, agencies require system...
Jun 28, 2022
When considering digital transformation initiatives, companies have plenty to consider. How will they reach their business goals? Will new technologies...
Jun 24, 2022
Over the last decade, DMI has proven to be a trustworthy partner to state and local government authorities, assisting with...
Jun 17, 2022
We believe you can read between the lines of 2022 Gartner® Magic Quadrant™ for Managed Mobility Services, Global and you...
Jun 16, 2022
Guest Post by Timo Loescher, Director, Strategy & Presales at DMICo-authored by Sara Trempe, UX Architect and Managing Consultant, Digital...
Jun 14, 2022
For the seventh year, DMI has been recognized as a Leader in the 2022 Gartner® Magic Quadrant™ for Managed Mobility...
Jun 9, 2022
Resourcing is top of mind for many companies, including financial and insurance service (FIS) organizations. The Great Resignation has made...
Jun 8, 2022
As federal agencies embrace cloud technology and automation tools, there is understandable excitement for how processes and workflows can be...
Jun 7, 2022
If you’re a state or local government leader considering a digital transformation project, you might be wondering what the journey–from...
Jun 3, 2022
When partners in the public sector need our help with a mission-aligned technological solution, DMI always begins with the people...
Jun 2, 2022
Everyone is talking about creating a composable architecture for your business. Daryl Plummer, VP, Distinguished Analyst & Gartner Fellow, notes...
Jun 1, 2022
Guest post by Lidia Romero, Account Director at DMI Global travel demand has reached its highest level since the pandemic’s...
May 27, 2022
The evolution of healthcare and its delivery has increased in pace substantially, well before the COVID-19 pandemic. One of the...
May 19, 2022
Change seems to be our new bedfellow in both our lives and the business world. While we continue to strive...
May 16, 2022
We are all too aware of the common patient-provider interaction. The most common scenario is the provider asking a question...
Apr 27, 2022
Today’s largest original equipment manufacturers (OEMs) in the automotive industry push over-the-air (OTA) software updates to 2 to 5 million...
Apr 25, 2022
The Department of Defence and other federal agencies have challenges when it comes to their IT...
Apr 12, 2022
Guest Post by Erin Krieger, Creative Director at DMI Your brand is the face, voice, and culture of your organization,...
Apr 11, 2022
Managed services have been crucial for many organizations, helping them run efficiently and embrace new technology without getting distracted from...
Apr 4, 2022
For retailers, “change” and “innovation” have historically been words only whispered in their halls and conference rooms – aspirations that...
Mar 28, 2022
The fourth industrial revolution, the blurring of boundaries between the physical, digital, and biological worlds, stands on the shoulders of...
Mar 24, 2022
The supply chain is a little like the lyrics of a song that say “(You) only miss the sun when...
Mar 23, 2022
Revenue teams are always buzzing about metrics that align with new customers. “What’s our acquisition rate?” “What’s our number of...
Mar 22, 2022
At one point in time, technology drove an organization’s strategy. Companies did their best to choose platforms that would provide...
Mar 21, 2022
Market disruption isn’t new in the financial services industry. It has, thanks to a number of technological factors, accelerated significantly....
Mar 20, 2022
As the existence and usefulness of recommendation engines have moved from the cutting edge of data science to the mainstream,...
Mar 17, 2022
Guest Post by Timo Loescher, Director, Strategy & Presales at DMI Building a strategy around digital transformation is a bold...
Mar 8, 2022
Guest Post by Timo Loescher, Director, Strategy & Presales at DMI It can appear that every company is currently undergoing...
Mar 3, 2022
For as long as there has been commerce, vendors have been considering how to present their merchandise to potential customers....
Feb 25, 2022
According to a recent study, global revenue for travel and tourism decreased by 34.7% during 2020. In 2021, the industry...
Feb 24, 2022
The benefits of being able to quickly and easily share healthcare data between providers are plentiful. Not only can it...
Feb 22, 2022
To say that the last decade has been a challenge for brick-and-mortar retailers is something of an understatement. Not only...
Feb 21, 2022
Globally, the number of mobile devices in 2020 stood at 14.02 billion, and by 2024, it is projected that the...
Feb 18, 2022
It’s no wonder that physicians are getting burnt out at increasingly higher rates. They work long hours and often feel...
Feb 16, 2022
Provider organizations, payer organizations, and healthcare companies typically use legacy IT business models. While these systems are traditionally reliable, they’re notoriously...
Feb 15, 2022
Recent advancements around the Internet of Medical Things (IoMT), medical devices, smart sensors, device manufacturing, and big data technologies have...
Feb 9, 2022
Amazon has set a high bar for everyone in the eCommerce and retail space. Consumers now expect free and fast...
Feb 8, 2022
Presently, every time you buy a new car, one of the first questions that arise is, “What can this thing...
Jan 31, 2022
Artificial intelligence and related concepts like autonomous robots are experiencing significant progress in recent years. Bots can perform tasks today...
Jan 28, 2022
There are many claiming that the last two years shook the retail industry, causing massive changes to brick and mortar...
Jan 26, 2022
Customer experience is top of mind for banking and financial services leaders. In the 2020 Digital Banking Report survey, financial...
Jan 25, 2022
Patient experience is critical to overall success in healthcare. Positive experiences can lead to an increased likelihood of better clinical...
Jan 24, 2022
Is the EV industry finally getting the support it needs from the community? It does raise awareness, but not without...
Jan 21, 2022
Imagine never again having to manually register your vehicle, punch in a keycode at a security gate, or stop at...
Jan 20, 2022
If there is an industry that understands the restrictions that come with legacy infrastructure and monolithic applications, it’s the banking...
Jan 18, 2022
Blockchain technology is not new. The idea of an immutable record was first created in 1991 when two researchers wanted...
Jan 17, 2022
The concept of digital transformation is about more than embracing modern technology. Through the careful integration of digital resources into...
Jan 14, 2022
While it’s certainly true that the pharma industry thrives on innovation, it’s also fair to say that it can certainly...
Jan 12, 2022
To be competitive, organizations need to realize the full potential of end-to-end automation. The term for unifying different technologies, platforms,...
Jan 10, 2022
Technology evolution in the healthcare industry is happening more rapidly than it has in the entire history of the sector....
Jan 7, 2022
When operating an organization in the 21st century, digital transformation has caused us to learn how to deal with disruption....
Jan 6, 2022
At its core, digital transformation is the process of integrating forward-thinking technology into all areas of an organization — something...
Jan 4, 2022
Regardless of its size or complexity, any state or local government can benefit from digital transformation. For starters, modernizing legacy... Dec 29, 2021
One of the major issues with legacy IT systems is that they ultimately end up costing organizations far more money... Dec 28, 2021
For years, everyone knew that a push towards digital services has been on the horizon for private businesses and government... Dec 27, 2021
One of the major reasons why digital transformation is so important is because it helps bring an organization from the... Dec 14, 2021
Industry 4.0 has been called many things, including “The Fourth Industrial Revolution.” While the technology behind this level of digital...
Dec 10, 2021
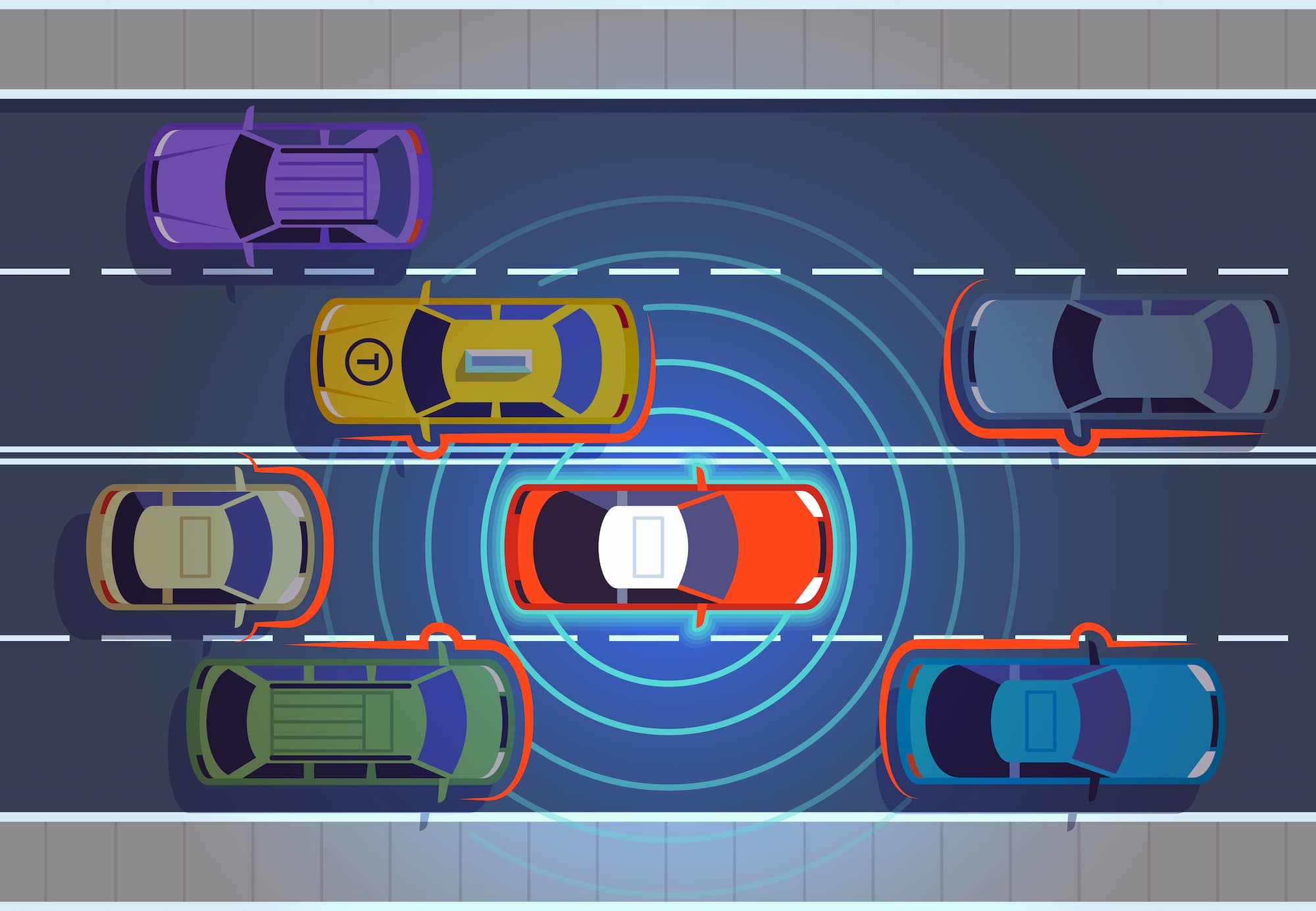
It wasn’t too long ago that people were asking when cars would drive themselves. Now, autonomous cars are becoming a...
Dec 8, 2021
The Internet of Medical Things (IoMT) poses unique technological challenges on two fronts: engineering and data science. All use cases...
Nov 16, 2021
Digital transformation is a pivotal change sweeping various industries, but its impact is perhaps most acutely felt in transportation. As...
Nov 2, 2021
The story of the Eastman Kodak Company is a cautionary tale for today’s businesses, including the insurance industry. Founded in...
Oct 28, 2021
Disruptors and changing federal requirements and guidelines are making it a “transform or die” environment for insurance providers and healthcare...
Oct 27, 2021
Just about everything in our economy has experienced some sort of change during the COVID-19 pandemic, and commerce is no...
Oct 25, 2021
Change is coming to the world of insurance. Learning that lesson requires looking at the insurance products and services that...
Oct 20, 2021
The global online travel agent market declined from $744.7 billion in 2019 to $595.8 billion in 2020 at a rate...
Oct 19, 2021
It is widely anticipated that airports will transition to touchless technology at a much quicker rate as a result of...
Oct 18, 2021
After a dramatic year for the hospitality ecosystem, global travel demand is at its highest since the beginning of the...
Oct 14, 2021
The way we travel is constantly evolving. Just a decade ago, if you wanted to go on a vacation, your...
Oct 14, 2021
If you had to make a list of some of the industries that have been heavily impacted by the ongoing...
Sep 23, 2021
There was a time when retail was relatively straightforward. Sure, a business would need to be concerned about inventory and...
Sep 21, 2021
The buzz for years has been around the imminent demise of brick-and-mortar stores, making room for online shopping experiences. Yet,...
Sep 9, 2021
Before many of us knew much about the Internet of Medical Things (IoMT), which is in essence connected medical devices,...
Aug 18, 2021
COVID-19 didn’t invent work from home, nor did it create mobility tools for businesses. In truth, mobility management isn’t an...
Aug 17, 2021
Fall is a wonderful time of year. The leaves begin to change, football season starts and the holidays are just...
Aug 10, 2021
Since 2000, over 790,000 mergers and acquisitions (M&A) have been announced worldwide, reaching a known value of over $57 trillion....
Jul 22, 2021
In light of the recent rise in ransomware attacks, The National Institute of Standards and Technology (NIST) has developed new,...
Jul 15, 2021
“Many government CIOs say their digital initiatives are maturing, but they often confuse progress with maturity,” according to Gartner. “[They]...
Jul 13, 2021
In 1848, California and the entire United States were changed forever following the discovery of a global natural currency: gold!...
Jul 8, 2021
The world changed in 2020. The rapid spread of COVID-19 and the subsequent shutdown and restrictions altered nearly everything about...
Jul 6, 2021
As previously discussed, detection is one part of defending against cyber threats within industrial automation control systems (IACS). After cybersecurity...
Jul 1, 2021
In this ever-changing world, the evolution of technology for enterprises and large businesses in Industrial Controls is growing rapidly. With...
Jun 29, 2021
At its core, cloud governance refers to a necessary framework that helps users make the most out of their cloud...
Jun 24, 2021
Even when a commerce enterprise isn’t looking at extreme platform challenges, the solution used to power this crucial part of...
Jun 23, 2021
Your contact center is one of the earliest touchpoints a customer has with your brand. A center supports customer interactions...
Jun 4, 2021
Business optimization is a recurring theme, no matter a company’s industry or size, and requires a constant dose of reinvention...
Jun 2, 2021
JBS Foods — one of the world’s largest suppliers of meat including beef, mutton and pork — recently suffered a...
May 25, 2021
For many businesses, cybersecurity is an abstraction that exists in the virtual world. Visualizing its impact in the physical realm...
May 17, 2021
Artificial Intelligence (AI) is the epitome of promise and excitement in technological advancements. We live in an era of unprecedented...
May 13, 2021
The technology behind traffic lights, hospital infrastructure, building operations and more is part of what is known as an Industrial...
May 11, 2021
On May 7, 2021, a major US energy transportation company known as Colonial Pipeline experienced a ransomware attack. This news...
May 6, 2021
One of the most important things to understand about the fast-paced modern era we’re now living in is that, while...
May 4, 2021
Recently, the Harvard Business Review examined more than 1,300 businesses that reported investing more than $100 billion in digital reinvention...
Apr 27, 2021
While most companies have adopted a digital-first business strategy or plan to do so, making a full-scale digital transformation is...
Apr 22, 2021
When people think of mobile devices, they often just think of smartphones. But “mobile” can refer to any device with...
Apr 20, 2021
Digital optimization is the process of using technology to improve existing operating processes and business models. It belongs at the...
Apr 19, 2021
Earlier this month, Gartner published the 2021 edition of the Magic Quadrant for Managed Mobility Services, Global. In it, DMI...
Mar 18, 2021
The Magic of Personalization Do you remember the first time you got a pop up on your phone letting...
Mar 16, 2021
As a marketer maybe I pay a little more attention to how brands are reaching their customers. However, you don’t...
Mar 16, 2021
We live in a time where we’re inundated with advertisements and brand messages throughout our day. From those social ads...
Mar 16, 2021
Personalization can seem like a daunting initiative to take on, but it has been done by many others before you...
Dec 14, 2020
In my previous blog post, I shared the story of how my plans for Christmas in 2020 were abruptly halted...
Dec 8, 2020
DMI is excited to announce that Mike Graziano recently joined our team as SVP Global Sales & Alliances, Digital Commerce....
Dec 7, 2020
Covid-19 has impacted nearly every industry, business and individual. It has forced large and small organizations alike to question how...
Dec 4, 2020
The MACH Alliance was launched in June 2020 and is rooted in the common belief that the interoperability and open...
Dec 2, 2020
This year has been unique and challenging for everyone as the global pandemic has forced us to adapt to new...
Sep 22, 2020
It is widely accepted that patient engagement is an important focus for our NHS. It is critical to achieve better...
Aug 20, 2020
The COVID-19 pandemic has changed the way we live and the way we work for the foreseeable future. Many workplaces...
Jul 22, 2020
The global pandemic has changed the way we work, socialize, and do business—and some of those changes are here to...
Jul 15, 2020
Healthcare companies have almost limitless opportunities to use digital tools to improve business outcomes. But it’s all beside the point...
Jul 14, 2020
Decisions about design patterns and dependencies can have a profound impact on the success of your move to cloud commerce....
Jun 23, 2020
Though all global industries are facing new pressures in light of COVID-19, the pharma and biotech sectors are feeling the...
Jun 18, 2020
Restrictions on retailing are starting to ease as government officials and public health experts gain more insight into the risks...
Jun 18, 2020
You don’t have to wait months or years to add automation to your supply chain. Many repetitive supply chain tasks...
Jun 17, 2020
Getting work done remotely gets more attractive every year, thanks to improvements in mobile device capabilities and expansion of network...
Jun 16, 2020
An elastic, cloud-based commerce environment has the potential to improve customer engagement and enhance website performance. …
Jun 12, 2020
A headless commerce system is a marvel of flexibility. You start by building an ideal frontend platform —the “head” that...
May 25, 2020
Business teams face huge pressure to build engaging mobile apps that will improve their customer experience, attract consistent feedback and...
May 20, 2020
It seems easy at first. People convene Zoom meetings from their living rooms and share documents on Microsoft Teams. But...
May 20, 2020
A headless architecture provides expansive options to fine-tune your customer experience. But flexibility has a cost: It takes a lot...
May 18, 2020
Moving to cloud-based commerce technologies requires learning new skills and mastering more nimble development methodologies. …
May 4, 2020
The value of remote work became clear as a health emergency spanned the globe. And it’s a fair bet that...
Apr 21, 2020
This is the third in a three-part blog series about the use of Magento. …
Apr 14, 2020
This is the third in a series of blogs about improving your call center. …
Apr 13, 2020
Shifting from a legacy commerce platform to cloud-based technologies requires a deft balance of skills, technologies and cost considerations. A...
Apr 9, 2020
Accelerated time-to-market is one of the best things about headless commerce. …
Apr 8, 2020
Cloud-native development can drive a wealth of business value — if you utilize the correct strategy. …
Apr 6, 2020
For all the terabytes of customer data brands collect around the clock, creating a personalized shopping experience can feel like...
Apr 1, 2020
This is the second in a series of blogs about improving your call center. …
Mar 30, 2020
This is the second in a three-part blog series about the use of Magento. …
Mar 19, 2020
In an era where customer expectations are at an all-time high, the role of advanced call center technology cannot be...
Mar 5, 2020
You can’t avoid every bump in the road to modernizing your e-commerce infrastructure. But you can anticipate the most common...
Feb 27, 2020
This is the first in a three-part blog series about the use of Magento. …
Jan 31, 2020
In an age where consumers are in control, brands have to work harder than ever to cut through the noise...
Jan 28, 2020
The appeal of a digital twin is obvious: You deploy a digital model that mimics real-world behavior — detecting inefficiencies,...
Jan 24, 2020
My Impressions of the 15th NRF Expo and Show As a technology professional focused on retail and commerce, this was...
Jan 15, 2020
Using predictive algorithms in customer care poses a challenge you might not anticipate: Accurate predictions don’t automatically generate better business...
Jan 8, 2020
They all have to come together — people and data, assets and inventions. …
Jan 2, 2020
It’s not enough to produce speed and value in Agile product development. You have to provide speed TO value in...
Blog2022-08-04T10:17:23-04:00